How A Whitehat Hacker Saved 109K ETH On SushiSwap-Based Contract
18 Agosto 2021 - 12:04AM
NEWSBTC
White hat hacker Samczsun from investment firm Paradigm reported
what could be one of the biggest rescues ever on the SushiSwap
protocol, the Ethereum ecosystem, and maybe the entire internet.
Just pulled off maybe the biggest whitehat rescue ever. Story time
soon 🔥 — samczsun (@samczsun) August 17, 2021 Samczun claimed in a
post that he found and help patch a vulnerability that was
threatening over $350 million or 109,000 ETH from a Sushiswap based
contract from its MISO platform. The white hacker reviewed the
contract after he found there was a new auction taking place on the
platform. MISO uses two types of auctions Duct and batch. While
Samczun was reviewing the DutchAuction contract, the white hacker
found that functions InitMarket and InitAuction lacked access
controls. This was “extremely concerning”. I didn’t really expect
this to be a vulnerability though, since I didn’t expect the Sushi
team to make such an obvious misstep. Sure enough, the
initAccessControls function validated that the contract had not
already been initialized. Samczun said that the above combined with
the use of a mixin library called BoringBatchable by the contract
made it more suspicious. The hacker recognized the ingredients that
led to an attack on another platform during 2020. Thus, Samczun was
able to identify that SushiSwap was in danger. If exploited, the
vulnerability would allow a bad actor to reuse a fixed amount of
ETH to batch multiple calls to the contract. This would effectively
allow the attacker to “bid in the auction for free”. While
processing token payments involved a separate transferFrom call for
each loop iteration, processing ETH payments simply checked whether
msg.value was sufficient. This allowed the attacker to reuse the
same ETH multiple times. Fixing A Multi-Million Dollar Bug On
SushiSwap In addition to free bids, a bad actor could steal the
funds on the SushiSwap contract by triggering a refund. The
attacker would have had only to send a higher amount of ETH than
the auction hard cap. Samczun said: This applied even once the hard
cap was hit, meaning that instead of rejecting the transaction
altogether, the contract would simply refund all of your ETH
instead. Just minutes after the white hacker discovered the
vulnerability, he put set up a “poor man’s mainnet fork on the
command line”. Thus, Samczun was able to verify if the contract
would allow for the above describe attack. Once the thesis was
verified, the white hacker reported the bug to SushiSwap’s CTO
Joseph Delong. He and other members of the protocol’s team
coordinated a response to remove the bug. The team and Samczun
“rescued” the funds by buying the remaining items. Thus, the
auction was finalized. As pseudonym community member DC Investor
said, the fact that the vulnerability was discovered by a white-hat
hacker from an investment firm with a high stake on Uniswap, the
decentralized exchange competing with SushiSwap, says a lot about
the “ethos” of the Ethereum ecosystem. DC said: Found and helped
patch a vulnerability that put over 109k ETH at risk everyone knows
Paradigm has big UNI / Uniswap bags, but Sam from their team just
helped save SushiSwap (an ostensible competitor) from a critical
bug this is the ethos of the space among the best actors. At the
time of writing, SUSHI trades at $12,50 with a 2.4% loss in the
daily chart.
Grafico Azioni Uniswap (COIN:UNIUSD)
Storico
Da Mar 2024 a Apr 2024
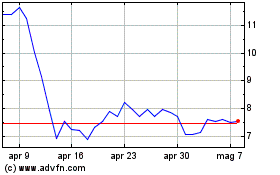
Grafico Azioni Uniswap (COIN:UNIUSD)
Storico
Da Apr 2023 a Apr 2024
